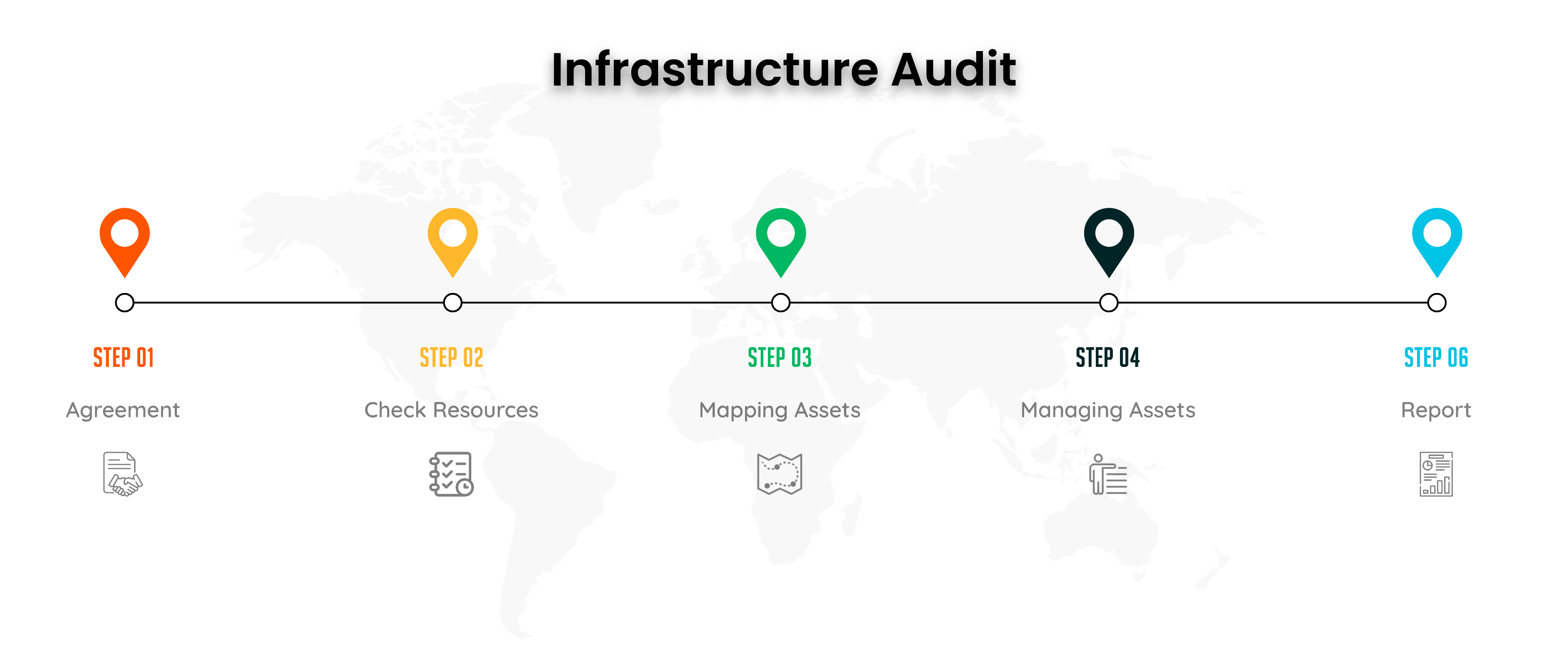
INFRASTRUCTURE AUDIT
INFRASTRUCTURE AUDIT WORKFLOW
Pre-Engagement
This stage includes essential aspects such as gathering the requirement and arranging meetings related to it while gathering information.
Information Gathering
This phase consists of gathering information associated with the target network infrastructure. The activities performed in this phase are Passive & Active Reconnaissance.
Outlining the scope
Once the required information is gathered, the detailed scope is outlined for assessment.
Vulnerability Assessment
It consists of profiling the target network infrastructure and assessing the target network infrastructure to identify vulnerabilities present using tools and manual techniques.
Exploitation
It involves actual steps involved in exploiting discovered vulnerabilities. During this, the stakeholders are intimately involved in allowing or disallowing the consultants to perform exploitation steps. The exploitation phase will cover all vulnerabilities outlined to the stakeholders and can be composed of vulnerabilities from external network devices and hosts.
Reporting Vulnerablity
Once the assessment is complete, a detailed written report outlinin`g each observed and or exploited vulnerabilities, along with the root cause analysis and categorisation along with mitigation and confirmatory re-test certificate if the need arrives.